TROLL TRIAD
An Archetypal and Group Psychology Troll Concept
Involving
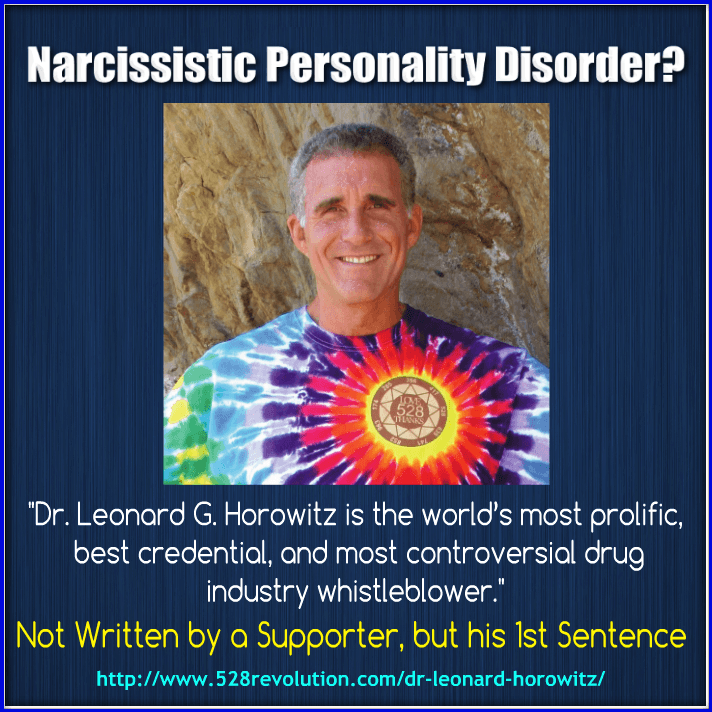
Dr. Leonard Horowitz, Sherri Kane & Michael Vara
by Michael Nuccitelli, Psy.D.
(Authored in 2014 but Still Educational & Relevant)
(TROLL TRIAD PDF DOWNLOAD HERE AND @ BASE OF PAGE)
Troll Triad was authored to inform online users about other online users who use internet defamation, libel and slander to control, manipulate and squelch others driven by needs for power and control or personal and financial gain. Troll Triad is not just about my trolls, Dr. Leonard Horowitz, Sherri Kane & Michael Vara; it is also an Information Age defamation, libel & slander group dynamic concept. As you will read, Troll Triad defines the roles members of a group portray to defame and slander their targets using Information and Communications Technology. Furthermore, the rationale for including Dr. Leonard Horowitz, Sherri Kane & Michael Vara is to compile an official record of evidence presenting their defamatory, slanderous and deceptive practices.
I provide here Exhibit-1, which compelled me to create this report. By clicking on the E-1 link and reading the first paragraph or two, you’ll understand why I’ve authored this investigative report. I recommend first reading here the definitions of Defamation, Slander & Libel authored by Cornell University Law School-Legal Information Institute [LII], the criteria for internet defamation & my internet defamation, libel & slander quick definition.
Exhibit-1 Link: Dr. Leonard Horowitz, Sherri Kane, Michael Vara E-1 File

DEFAMATION
Cornell University Law School-Legal Information Institute [LII]
“Defamation is a statement that injures a third party’s reputation. The tort of defamation includes both libel (written statements) and slander (spoken statements). To win a defamation case, a plaintiff must show four things: 1) a false statement purporting to be fact; 2) publication or communication of that statement to a third person; 3) fault; and 4) damages, or some harm caused to the person or entity who is the subject of the statement. Since the U.S. Supreme Court’s 1964 decision in New York Times v. Sullivan, defamation claims have been limited by First Amendment concerns. Thus, for instance, public officials and public figures (people who are famous) must show that statements were made with actual malice to recover in an action for defamation. Actual malice means that a statement was made with knowledge that it was false or with reckless disregard of whether or not it was false. In addition, a plaintiff must show actual malice by “clear and convincing” evidence rather than the usual burden of proof in a civil case, preponderance of the evidence. A private person suing about a matter of private concern need only show negligence, meaning that the defendant knew the statement was false, or would have known if she or he had exercised reasonable care. Defamation claims are also subject to a number of privileges. The types and limits of these privileges will vary from state to state. An absolute privilege is a complete defense to a defamation claim. For instance, statements made by witnesses during judicial proceedings are subject to absolute privilege. The reason is that those statements are subject to sanctions. An absolute privilege also protects statements made during legislative debates. A qualified privilege may also protect statements. For instance, a parent’s statement to her or his children warning them not to associate with certain kids is likely protected by a qualified privilege.” Cornell University Law School-Legal Information Institute [LII]
Criteria for Internet Defamation
- The statement(s) in question is a false statement, but intentionally or negligently presented and disseminated as a statement of fact.
- The statement(s) in question is a false statement of fact that causes harm or designed to cause harm to the subject or the subject’s reputation.
- The statement(s) in question is a false statement of fact causing harm to the subject or the subject’s reputation and was made without research to verify the truthfulness of the statement.
- The statement(s) in question is a false statement of fact causing harm to the subject or the subject’s reputation, who is a public figure or celebrity, and the false statement of fact is maliciously published online to do harm or acted in a reckless manner.
Internet Defamation, Libel & Slander Quick Definition
Internet Defamation (aka, Online Defamation) is a felonious statement of fact using Information and Communications Technology (ICT) that is published or disseminated to a third party in a careless or intentional manner and causes injury or damage to the subject of the statement. Internet Libel and Slander are different types of Defamation. Libel is a written defamatory statement, and slander is an oral defamatory statement. As mentioned above, Troll Triad was authored to introduce my concept describing how groups of three or more online users assume archetypal roles in tasks when attempting to defame, slander and attack another online user’s reputation, online presence or business.
One would think being the author of the dark side of cyberspace construct, iPredator, and being regularly internet trolled and harassed as the founder of iPredator Inc., viewing his baloney would be no different from any other proverbial day at the office. For whatever reason, seeing Horowitz’s ludicrous 177-page manifesto that was addressed to the NYS Office of Professional Discipline and then learning Mr. Vara was encouraging his internet radio listeners to read his nonsense on air is when the Nuccitelli blood began to boil.
After watching back-to-back documentaries of Sun Tzu’s “Art of War” on YouTube, I sat down in front of my computer and authored this paper. In this manuscript, the information presented about Dr. Leonard Horowitz, Sherri Kane & Michael Vara is not misleading, false or altered in any manner to support the paper’s objectives. I was sure not to portray them in a false or misleading light. There is no information that would be offensive or embarrassing to a reasonable person of ordinary sensibilities. Furthermore, as the author, I was cognizant at all times that the content contained herein would not be defamatory, copyright infringement or a breach of privacy.
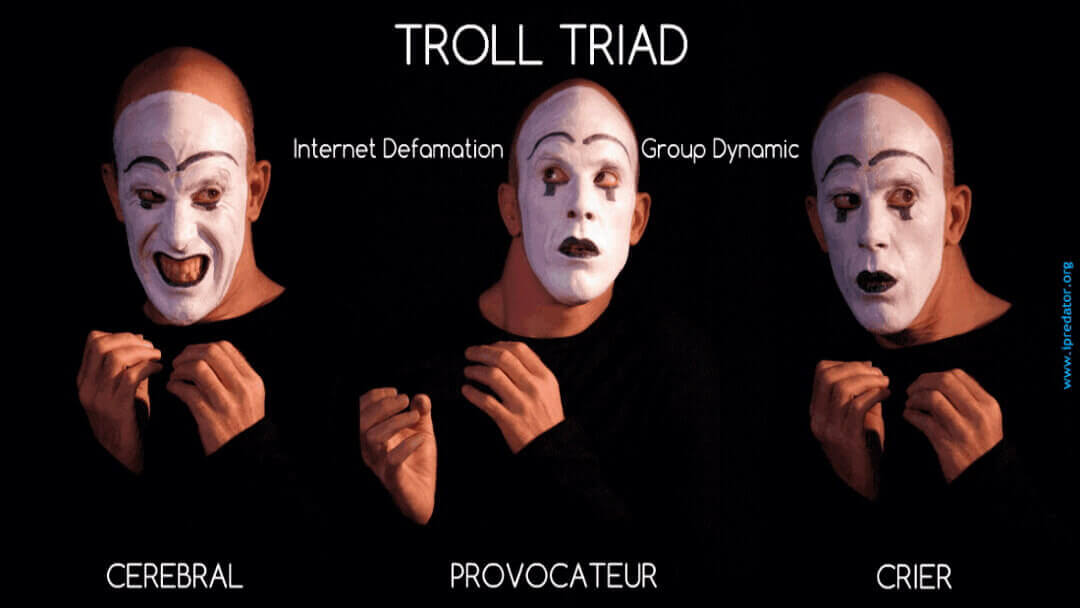
Troll Triad is a cyber psychopathology-profiling construct that introduces a three-pronged archetypal model defining groups of online users who engage in defamation of character, slander & libel. As stated above, Troll Triad is not just a facetious term describing three small minded online users who use Information and Communications Technology to defame, manipulate, curry favor and seek support from other like-minded online users.
Troll Triad is also a conceptual framework and template describing how future groups of successful iPredators will be partitioned into three archetypal segments. This troika includes the Cerebral, Provocateur and the Crier. When these three elements mix correctly, the Troll Triad becomes a masterpiece of human predation alchemy. Being a disciple of Carl Jung and Alfred Adler, I strongly subscribe to Jung’s theory of Archetypes and Adler’s theory of Social Interest. Using their constructs as guidelines, Troll Triad is a concept relevant to the Information Age.
This paper also serves as a personal journal of record documenting the persistent Character Assassinations I’ve experienced by three online acquaintances named Leonard Horowitz, Sherri Kane & Michael Vara. I’ve never met any of them face-to-face, but Michael Vara is the one I was closest too having been a regular guest on his internet radio show from 2011-2014. Leonard Horowitz and Sherri Kane I hardly know having spoken to them on a couple occasions through Michael Vara. It wasn’t until Michael Vara and I parted ways in August 2014 is when the disinformation and defamation attacks began.
It was then that I learned about Michael Vara’s cohorts, Dr. Leonard Horowitz and Sherri Kane spearheading the project. It’s ironic that the product of their bizarre and preposterous attempts to defame my character led to this concept being born. I guess in some odd way I should thank them for providing the fodder to help lay the foundation of the Troll Triad concept. In the manuscript that follows, I attempt to meet the following objectives:
- Introduce brief definitions of the three Troll Triad typologies, which are the Cerebral, Provocateur and Crier Archetypes.
- Present a bullet list of exhibits and evidence confirming Dr. Leonard Horowitz, Sherri Kane & Michael Vara are actively engaging in Copyfraud, Defamation, Slander and Online Deception.
- Provide a list of iPredator definitions relevant to fully understanding the first two objectives and the central themes of iPredator Inc. internet safety initiatives
“Although federal, state, and local officials work diligently to combat iPredators, their endeavors are minimal at best given the size of the iPredator contingent. iPredators have the luxury of trolling for their victims at a leisurely pace without fear of identification, confrontation, and punishment.” Michael Nuccitelli, Psy.D. (2011)
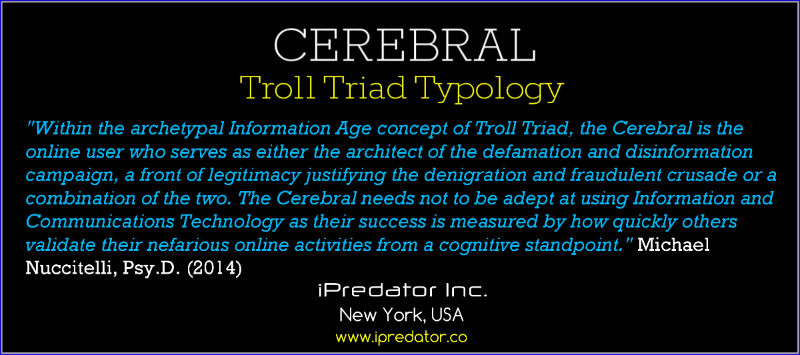
TROLL TRIAD CEREBRAL
Within the archetypal Information Age concept of Troll Triad, the Cerebral is the online user who serves as either the architect of the defamation and disinformation campaign, a front of legitimacy justifying the denigration and fraudulent crusade or a combination of the two. The Cerebral does not need to be adept at using Information and Communications Technology as their success is measured by how quickly others validate the group’s nefarious online activities from a cognitive standpoint. The Cerebral does not have to be formally educated with advanced academic degrees, so as long as they are charismatic and intriguing in online or offline public forums. The Cerebral is best described as the “brains of the online operation”.
Whether the Cerebral is 1 person or 1001 people, their goal is to rationalize successfully to others, using their intellectual prowess, validation why the Triad must defame and destroy their target. The Cerebral is least likely of the Triad to display fits of anger or rage in offline and online forums. It is in private and with other Triad members when they feel secure enough to release their internal feelings of rage and discontent.
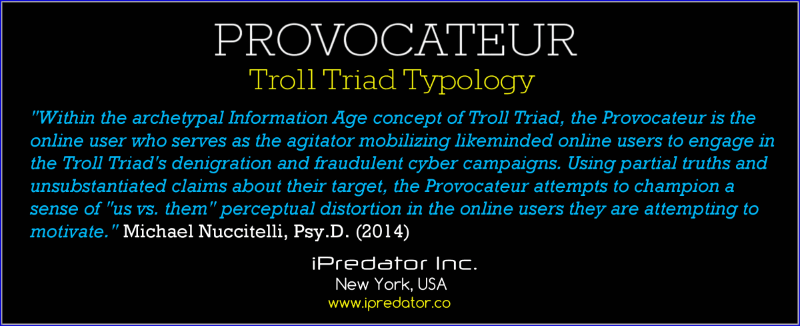
TROLL TRIAD PROVOCATEUR
Within the archetypal Information Age concept of Troll Triad, the Provocateur is the online user who serves as the agitator mobilizing other like-minded online users to engage in the Troll Triad’s denigration and fraudulent defamation campaigns. Using partial truths and unsubstantiated claims about their target, the Provocateur attempts to champion a sense of “us vs. them” to instill their perceptual distortion in the online users they are trying to motivate. The Provocateur serves four primary functions.
- Motivate and mobilize as many like-minded online users as possible to become active participants in the defamation campaigns.
- Create, disseminate and motivate like-minded online users by using details about their target to justify their campaigns.
- Actively and persistently, exonerate and espouse accolades about the Cerebral to create a pseudo-moral justification for attacking their target(s).
- Provoke and incite as many like-minded online users as possible by using partial truths, total fabrications and unsubstantiated claims ranging from mildly embellished to completely
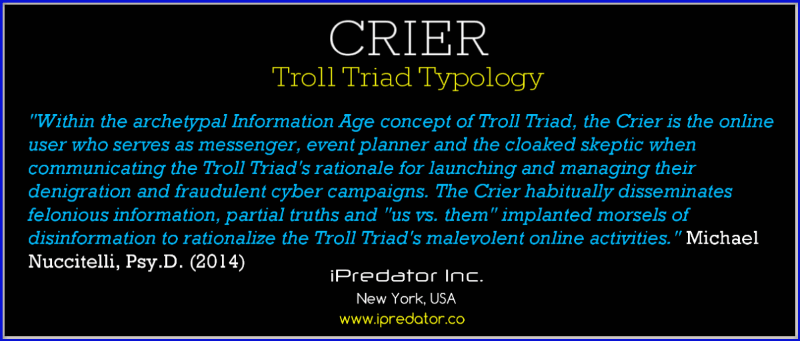
TROLL TRIAD CRIER
Within the archetypal Information Age concept of Troll Triad, the Crier is the online user who serves as messenger, event planner and the cloaked skeptic when communicating the Troll Triad’s rationale for launching and managing their denigration and fraudulent defamation campaigns. The Crier habitually disseminates felonious information, partial truths and “us vs. them” implanted morsels of disinformation to rationalize the Troll Triad’s malevolent online activities.
Within the Troll Triad, the Crier is least likely to be the most intelligent, provocative or charismatic as the Cerebral and Provocateur. Where the Crier is more adept and skilled than the other two is in their ability to spread the Triad’s message. Not only is the Crier the most effective messenger of the three typologies, but they also serve as the group’s cloaked skeptic. Although their objectives to disparage and defame a target are the same as the Cerebral and Provocateur, the Crier works to validate the Cerebral’s intellect and the Provocateur’s passion by presented alternative views and insights. When done effectively, the Crier not only further motivates like-minded online users, but also encourages online users who are not yet committed to join their defamation and disinformation campaigns.
The Cerebral, Provocateur and Crier typologies in the Troll Triad are archetypes and segments of groups who are allied in a mission to defame, disparage and destroy their target’s online reputation and trust. The Troll Triad is an archetypal model that can describe three like-minded people or an entire nation bound by the same goal of harming others. In relationship to my trolls, Dr. Leonard Horowitz, Sherri Kane & Michael Vara, it does not take long to identify each of their positions quickly within the Troll Triad.
Dr. Leonard Horowitz is the Cerebral. Sherri Kane is the Provocateur and Michael Vara is the Crier. Working as a united front, these three people represent amateur rudimentary models of the Troll Triad. If they were truly adept at their Triad functions, I would not have been successful at securing 1/10 of the evidence and data verifying their disinformation and defamatory practices. From a macroscopic perspective, they are nothing more than angry adults who desperately want to be recognized.
However, they do have access and support from other like-minded online users who are willing to participate in their denigration and fraudulent cyber-attack campaigns. You will not find any of their minions ever questioning their motivations for attacking others or espousing their ludicrous theories. As you will learn in the exhibits presented below, Horowitz, Kane & Vara are working as a system that closely follows the three Troll Triad archetypes.
“By virtue of the proverbial cloak of anonymity so conveniently provided by Information and Communications Technology, iPredators troll cyberspace with a distinct advantage in that they may represent themselves in any way they choose.” Michael Nuccitelli, Psy.D. (2011)

Troll Triad Note: As of January 2015, and assuredly moving forward; Dr. Leonard Horowitz, Sherri Kane, Michael Vara and their blind faith supporters will continue to defame and slander others they fear may expose their deceptive practices and delusional ideologies. In relationship to myself and iPredator Inc., I’m confident they will continue to invent preposterous stories of covert campaigns I’m spearheading to shut down their websites, shows, social accounts and whistle blowing pursuits.
Unlike their typical targets who fear retribution and public backlash if they assert themselves, I revel at the chance. Although I’ve compiled an enormous database of evidence all pointing to them and their followers as being the source of these attacks, I’m ethically bound to say the information contained herein are allegations until a court of law makes the final determination. A recommendation to the Troll Triad, since I guarantee they will be reading this paper. Every professional who has scanned your information to date concluded your clueless when it comes to defamation laws, and our first amendment freedom of speech. Here are a couple links to get you started.
- New York Defamation Laws
- South Carolina Defamation Laws
- Hawaii Defamation Laws
- Idaho Defamation Laws
- Section 230 of Title 47 of the United States Code (47 USC § 230)
- Amendments to the Constitution of the United States
- The Constitution of the United States-PDF
“As humanity becomes more dependent on Information and Communications Technology, we slowly isolate and disconnect from human contact on a real human and spiritual level.” Michael Nuccitelli, Psy.D. (2011)
TROLL TRIAD EXHIBITS
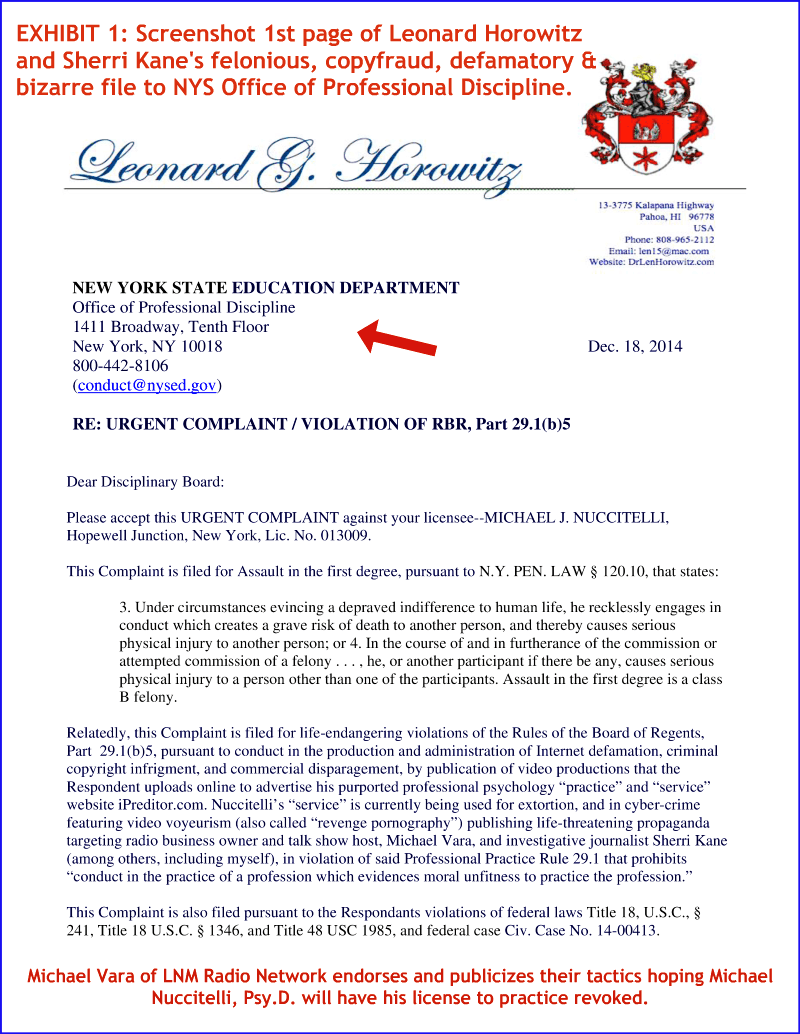
EXHIBIT-1: E-1 is a screenshot of the first page from the 177-page complaint sent to the New York State Education Department; Office of Professional Discipline dated December 18, 2014. Signed by Dr. Leonard Horowitz (E-3) and cc’d to Sherri Kane and Michael Vara, the obvious purpose of this document is an attempt to defame my character and inhibit my ability to practice in New York State. Of all the exhibits compiled, E-1 is by far the most heinous of defamation and disinformation tactics launched by Dr. Leonard Horowitz, Sherri Kane & Michael Vara.
The document’s content is best described as bizarre and authored with a paranoid driven mind. E-1 provides evidence that Dr. Leonard Horowitz, Sherri Kane & Michael Vara are engaging in copyfraud, slander & gross disinformation practices. This document is also one of the three files deleted by Scribd on December 23, 2014 after Dr. Leonard Horowitz uploaded and published this nonsense in Scribd’s database. Provided here are links the WebMD Delusional Disorder page and my copy of the Horowitz Copyfraud File. Please note that the complaint copy is in my possession and you will not be directed to any of their sites to review or download.
Link: WebMD Delusional Disorder Page
Link: Dr. Leonard Horowitz, Sherri Kane, Michael Vara E-1 File
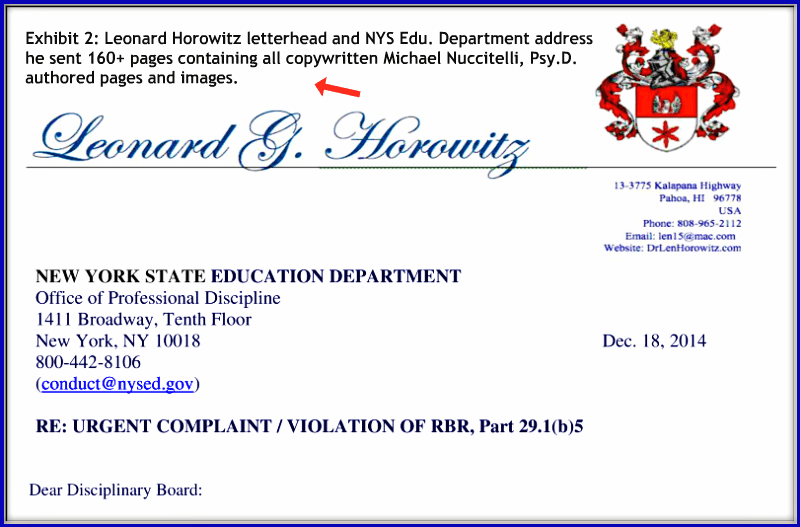
EXHIBIT-2: E-2 is a screenshot of Dr. Leonard Horowitz’s letterhead he used to send his 177-page delusional file to the NYS Education Department & Office of Professional Discipline. E-2 is part of a broad evidentiary database verifying Dr. Leonard Horowitz intentionally initiated a formal complaint using copyfraud, defamation & felonious files for malevolent reasons. Given he cc’d (carbon copied) this document to Sherri Kane and Michael Vara, who are both actively disseminating this report online, all three are engaging in Copyfraud, Slander, False Light & Disinformation.
Link: Dr. Leonard Horowitz, Sherri Kane, Michael Vara E-1 File
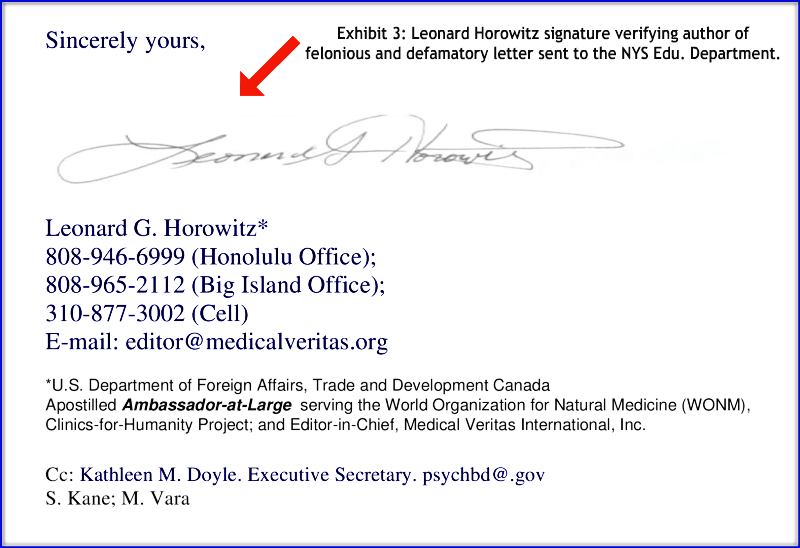
EXHIBIT-3: E-3 is a screenshot of Dr. Leonard Horowitz’s signature verifying he is the author of my copyfraud, defamation & disinformation document sent to the NYS Education Department & Office of Professional Discipline.
Link: Dr. Leonard Horowitz, Sherri Kane, Michael Vara E-1 File
“Cyberstealth is a method and strategy by which a child, adult, group or nation uses Information and Communications Technology (ICT) to establish and sustain complete, partial or divisive anonymity while they troll, stalk and attack their target(s). To ensure success, cyberstealth employs online deception, social engineering and disinformation to distract and confuse their target(s). Given the Internet inherently affords everyone anonymity, Cyberstealth used by iPredators (aka, online assailants) range from negligible to highly complex and multi-faceted.” Michael Nuccitelli, Psy.D. (2014)
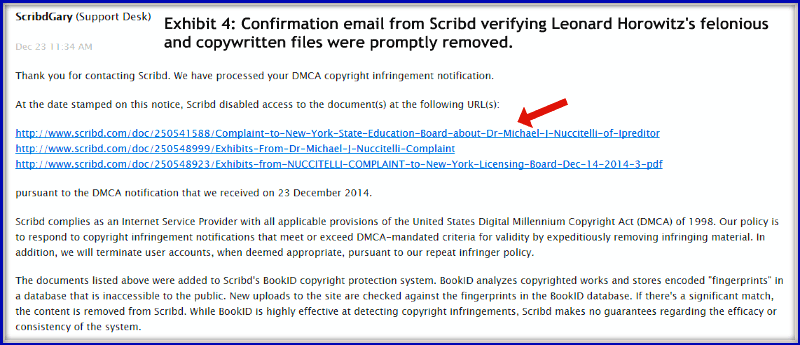
EXHIBIT-4: E-4 is a screenshot of the confirmation email from Scribd to myself verifying Dr. Leonard Horowitz, Sherri Kane and Michael Vara’s copyfraud, defamation and felonious files were deleted on December 23, 2014. Using the Scribd username of Legal Evidence, Horowitz uploaded three variations of their 177-page bizarre complaint, used different permalinks for each file, then made them all public and search engine crawlable. Thanks to Google Alerts, I received an email and found his data.
Given Scribd is very proactive when members breach their guideline, I wrote them and his bizarre documents were promptly deleted. In addition to removing Horowitz’s psychotic prose, Scribd will now track and monitor his accounts whether he has one or 101 usernames. Typical of cowards, you could not find his name anywhere attached to his Legal Evidence username without doing a little leg work. A little research was performed, and iPredator Inc. has confirmed Dr. Leonard Horowitz, Sherri Kane and Michael Vara were all aware of the files being uploaded and posted. Thanks to Scribd, they all now have to explain why those links are dead to their minions. Provided here is my secured copy of the Triad’s defamatory and copyfraud document that was uploaded three times in Scribd with different tags and permalinks.
Link: Dr. Leonard Horowitz, Sherri Kane, Michael Vara E-1 File
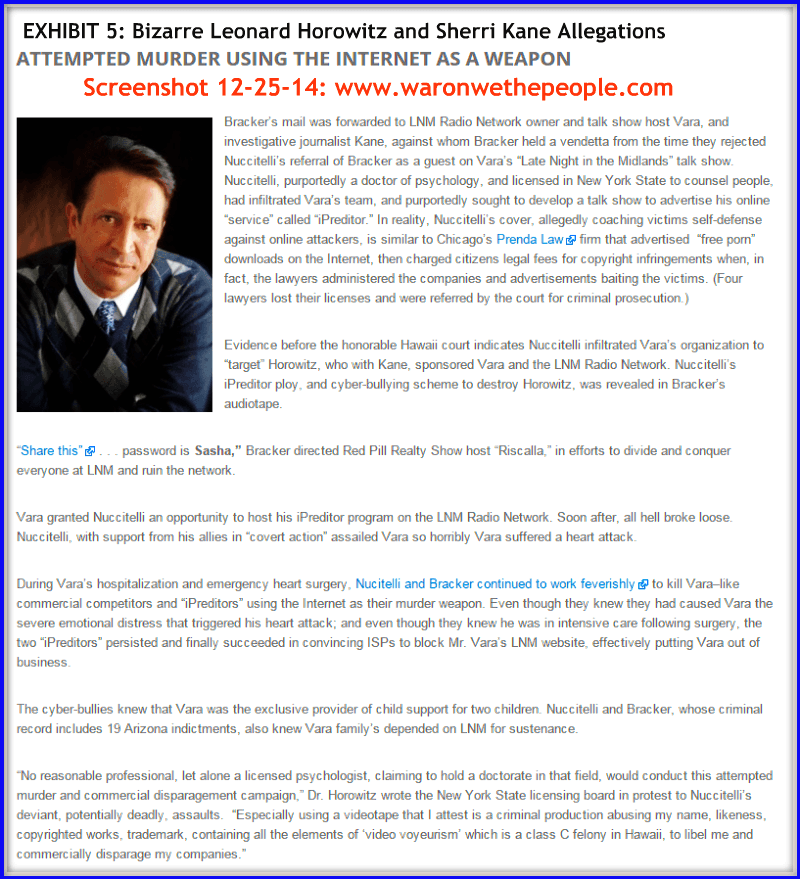
EXHIBIT-5: E-5 is an image of the Michael Nuccitelli, Psy.D. content that was authored and published by Dr. Leonard Horowitz and Sherri Kane on December 18, 2014. Their web page article is titled, “NSA Trained Domestic Terrorists Caught Covert Action” and available at Dr. Leonard Horowitz and Sherri Kane’s website, “War on we the People”. As of January 3, 2015, their page and the delusional article are live. For those interested in reading this content, if it is been deleted or removed provided here is a link to my secure copy of that page that was captured on December 31, 2014. When the link opens, use your image enlarge feature if the text is too small to read. As you are reading their nonsense, please don’t forget that Michael Vara of LNM Radio Network actively disseminates their information and encourages his listeners to read as well.
Link: War On Us the World Delusion Web page Image
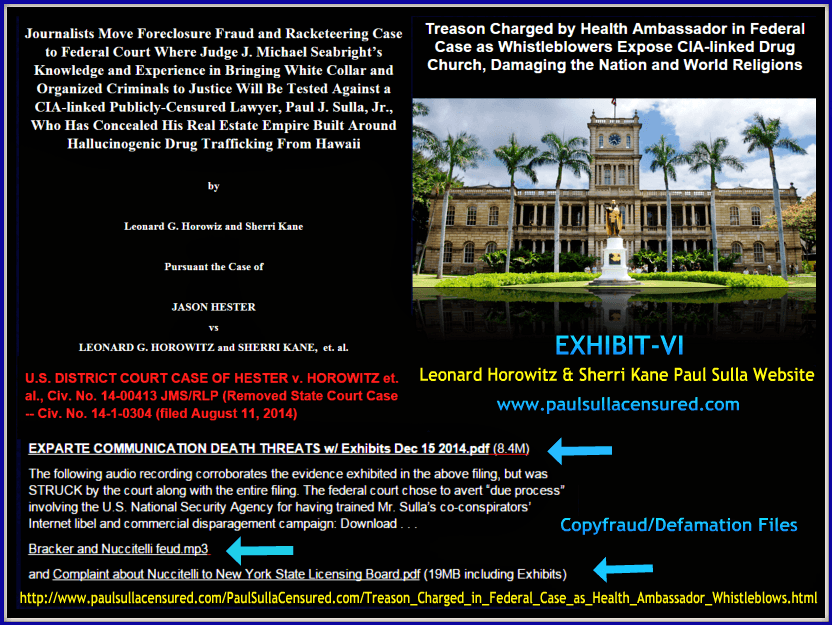
EXHIBIT-6: E-6 is a collage image of screenshots I compiled from Dr. Leonard Horowitz and Sherri Kane’s website, www. Paul Sulla Censured dot com. Hidden among their pages of paranoid themed content, I was able to locate and secure the original copy of Horowitz file that was sent to the NYS Education Department. Although their “Paul Sulla Censured” domain is hosted by a hosting company in the Bahamas and privately registered, iPredator Inc. was still successful in confirming Dr. Leonard Horowitz and Sherri Kane as domain owners.
As I will not contribute to their website’s page ranking, by posting the link here to click on, interested parties can visit the link that is included at the base of the image. If you want to read more about their bizarre and often psychotic content, just copy and paste this term with quotes in Goggle and hit search “Paul Sulla Censured”. Welcome to the Schizophrenic world of the Troll Triad named, Dr. Leonard Horowitz, Sherri Kane & Michael Vara.
“Online deception is an art and science of effectively mixing truth, observation and accepted assumptions with felonious conclusions, illusions and lies. When combined with a veil of anonymity in cyberspace, the final preparation becomes a dish impossible to refuse by the growing population of information addicted gluttons called humanity.” Michael Nuccitelli, Psy.D. (2014)
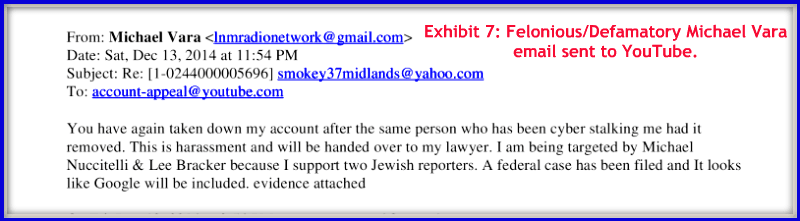
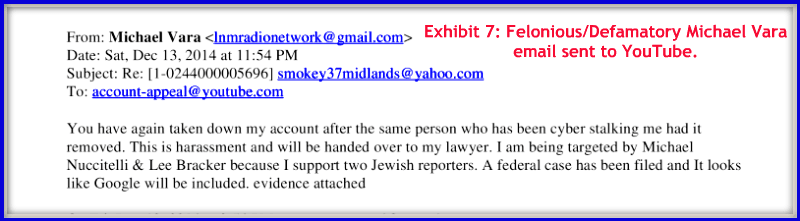
EXHIBIT-7: Collected from Dr. Leonard Horowitz and Sherri Kane’s copyfraud, defamation, & felonious master document, provided here is a screenshot of Michael Vara’s email, dated December 13, 2014, responding to YouTube after they deactivated his YouTube Channel. In his desperate attempt to restore his channel, Michael Vara engages in gross deception by alleging I am cyberstalking and cyber harassing him. His weak excuses would not be so laughable if he did not know the difference between the two or their definitions. Is it possible that being a guest on his show 15-20 times and having had 100-150 phone conversations over a 3-year period that he still not know what they mean?
You would think he would know the definitions given he now states that he is an internet safety expert with years of experience dating back to 1999. He presents this information in his G+ account and is available for helping others who’ve been targeted online. The part that bothers me about this email is how he implies I’m Anti-Semitic. I have to assume he is referring to Dr. Leonard Horowitz and Sherri Kane. The importance of publishing this small message and image here is because it is foreshadowing the Troll Triad’s future defamatory theme. I guarantee within 6-8 weeks of editing this page, the Troll Triad will respond to wild allegations ranging from me being a white supremacist to holding a high positioned officer in the Neo-Nazi movement.
“Now where is the picture of Dystopia more clearly depicted than through the literary genre of science fiction. Expressed in the works of prophetic writers such as Ray Bradbury, Aldous Huxley, and George Orwell, humanity becomes increasingly separate from one another led by technology.” Michael Nuccitelli, Psy.D. (2014)
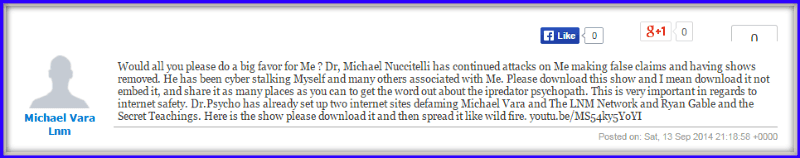
EXHIBIT-8: E-8 is a screenshot image of Michael Vara, on September 13, 2014, seeking help by posting on a classified website called, Express Topics. In his request, you’ll notice he sounds desperate in his endeavor to find anyone to download and store his August 28, 2014 show. The apparent urgency Michael Vara communicates is due to, as he writes, is because I am an iPredator psychopath, cyberstalker and attempting to shut down his website and show. If this is Michael Vara, it speaks to his weak character and hidden online activities. If it is not him and a supporter or listener is the culprit, it speaks to the type of audiences he attracts to his show and social accounts. The author of this message implies that a ridiculous internet radio show is so valuable that it needs to be secretly stored for protection.
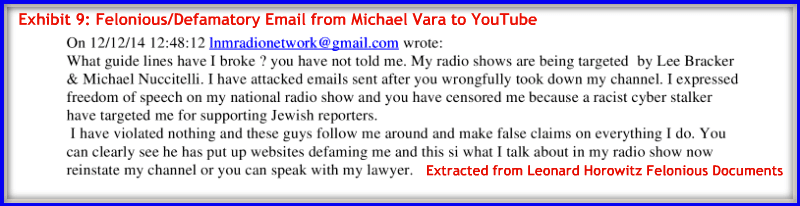
EXHIBIT-9: Collected from Dr. Leonard Horowitz and Sherri Kane’s copyfraud, defamation, & felonious master document, provided here is a screenshot of Michael Vara’s email. Dated December 12, 2014, Michael Vara is responding to YouTube after they deactivated his YouTube Channel. Michael Vara engages in gross disinformation again by stating, I am a “Racist Cyberstalker” because he supports Jewish reporters. Precisely as illustrated in Exhibit-7, Michael Vara again is forecasting the theme that he, Dr. Leonard Horowitz and Sherri Kane will be using in the near future.
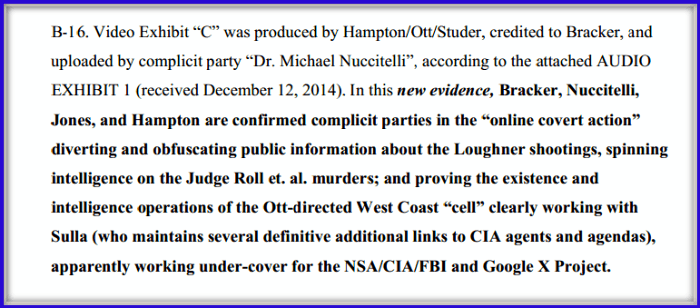
EXHIBIT-10: Collected from Dr. Leonard Horowitz and Sherri Kane’s copyfraud, defamation, & felonious civil lawsuit, provided here is a screenshot image captured from Dr. Leonard Horowitz and Sherri Kane’s (CIV. NO. 14 00413 JMS/RLP) civil action, which they have been pushing in the courts for years. Not knowing Dr. Leonard Horowitz or Sherri Kane, other than my brief interactions with them through Michael Vara, I canot connect the dots to see how I’m part of a civil action involving people I know nothing about. From my research, I can only surmise that Dr. Leonard Horowitz and Sherri Kane are being deceptive by including me in their bizarre lawsuit to bolster their divisive agendas with the Hawaiian Courts.
Link: December 2014 Troll Triad Civil Action
“Although I view the World Wide Web, Telecommunications, Digital Technology and Mobile Device Technology as highly beneficial tools and areas helpful to society, I do recognize tools have many different purposes. When chosen for nefarious reasons, Information and Communications Technology are tools that become lethal weapons.” Michael Nuccitelli, Psy.D. (2011)
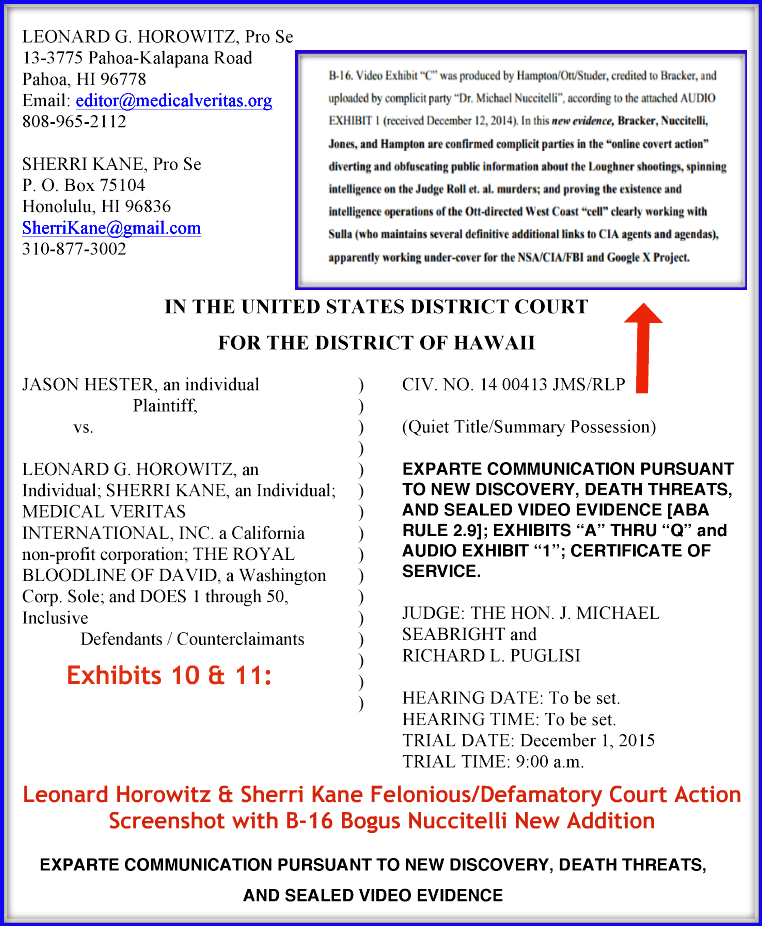
EXHIBIT-11: E-11 is a screenshot image of Dr. Leonard Horowitz and Sherri Kane’s (CIV. NO. 14 00413 JMS/RLP) court suit combined with my EXHIBIT-10 screenshot image. Again, this image verifies Dr. Leonard Horowitz; Sherri Kane and Michael Vara have falsely included me in their preposterous and bizarre lawsuit. Please note that the Troll Triad is fully aware of their deceptive practices and at the time of my authoring this paper, I guarantee they think I am doing nothing to address their nonsense. Let us see what the near future brings as to my apathy in relationship to their defamatory and deceptive practices. Provided, here again, is a link to my secure copy of their December 2014 waste of taxpayer money legal documents.
Link: December 2014 Troll Triad Civil Action
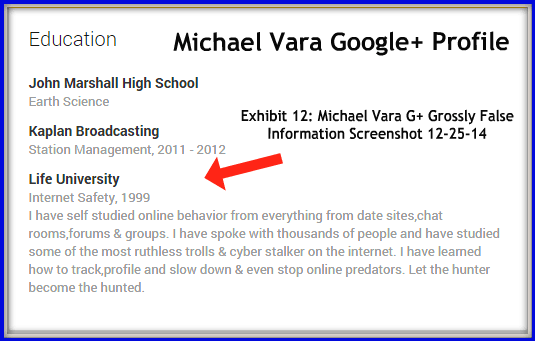
EXHIBIT-12: E-12 is a screenshot image of Michael Vara’s Google Plus profile education section, captured on December 25, 2014, and still live at the time of this writing on December 31, 2014. As you can see, Michael Vara falsely claims he is an internet safety professional who has spoken to thousands of people and has studied online behavior since 1999. I laugh at myself every time I read his felonious statements because I quickly recall past LNM shows I was a guest educating his listeners on the dark side of cyberspace and pervasive online deception. I distinctly remember Michael Vara frequently commenting on how growing numbers of online users weave incredible tales about themselves and their careers. As you can read in the above image, it seems Michael Vara is a professional at online deception.
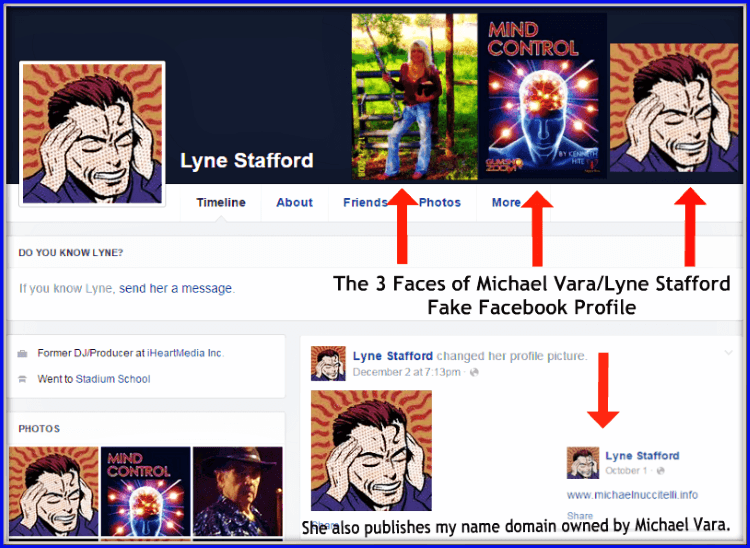
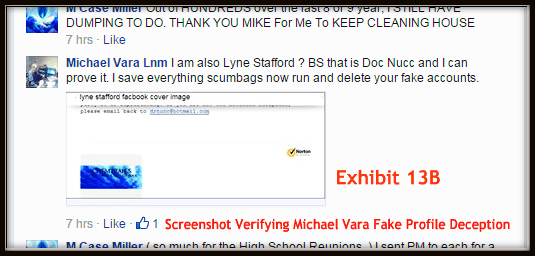
EXHIBIT-13: E-13 is a screenshot image of Michael Vara’s felonious Facebook profile, Lyne Stafford. Michael Vara has always denied being the profile owner of Lyne Stafford and that she was owned and operated by yours truly. A previously secured screenshot verifies Michael Vara telling a Facebook friend he will prove I am the owner of Lyne Stafford. Apparently, Michael Vara has presented no proof to date after 2+ months. It also should be noted; showing Michael Vara is Lyne Stafford is that Lyne Stafford posted the Michael Vara owned www dot Michael Nuccitelli dot info domain on her Facebook wall. As of January 3, 2015, click on the link and see where it brings you at the LNM Radio Network website.
Link: www.MichaelNuccitelli.info (404 Page)
Update 1-31-15: As of 1-31-15, Michael Vara’s Nuccitelli domain, not only no longer points to his LNM Radio Network website Radio Guest Troll page, but he has either hidden or removed this page: http://latenightinthemidlands.com/radio-guest-troll-tactics/. At present, his link comes back as a 404 page. This domain is not mine and is owned by Michael Vara. The domain points to the LNM Radio Network Radio Guest Troll Tactics page, which he alleges I stole my pediatric internet safety character, Troll Man from. As you can see in the lower right-hand corner of my image, the red arrow points to an overlay image from October 1, 2014 verifying Lyne Stafford publicly posted his Michael Nuccitelli domain. In the image 13B above, here is the evidence Michael Vara lying once again.
“The “veil of invisibility” Information and Communications Technology and cyberspace offers humanity has numerous benefits, but the detriments can far outweigh the assistances for the vulnerable, unaware or ignorant online user.” Michael Nuccitelli, Psy.D. (2011)
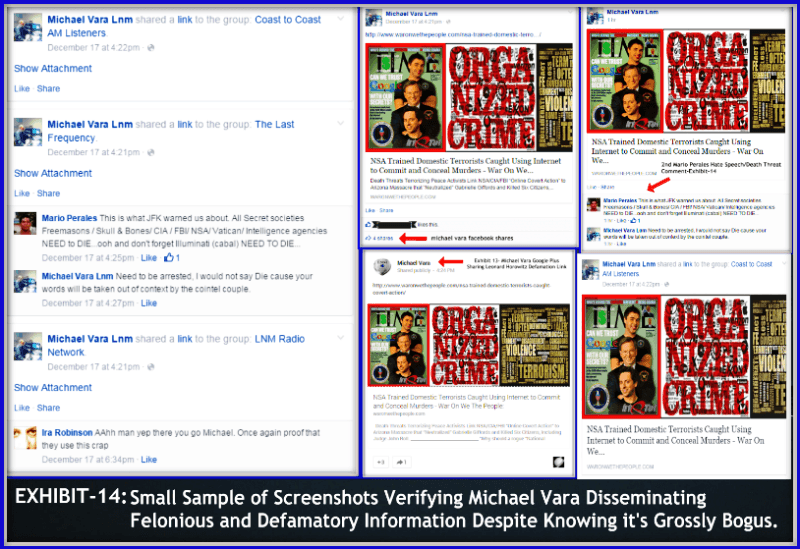
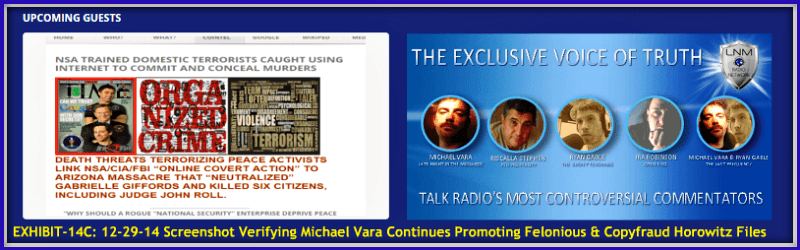

EXHIBIT-14: E-14 is a screenshot collage image verifying Michael Vara’s active dissemination and sharing of Dr. Leonard Horowitz and Sherri Kane’s copyfraud, defamation and felonious bizarre files. Within 24 hours of Horowitz finishing his bogus report, you can plainly see Michael Vara shared the links at a feverish pace. Screenshot images, 14B & 14C, are additional screenshots of Michael Vara’s sharing frenzy. I thought about publishing other exhibits of him sharing the news, but I figured six examples prove my point. Having been a close associate to Michael Vara for over three years, there is no doubt that he is fully aware of disseminating felonious information that is bizarre, unlawful and extremely defamatory.
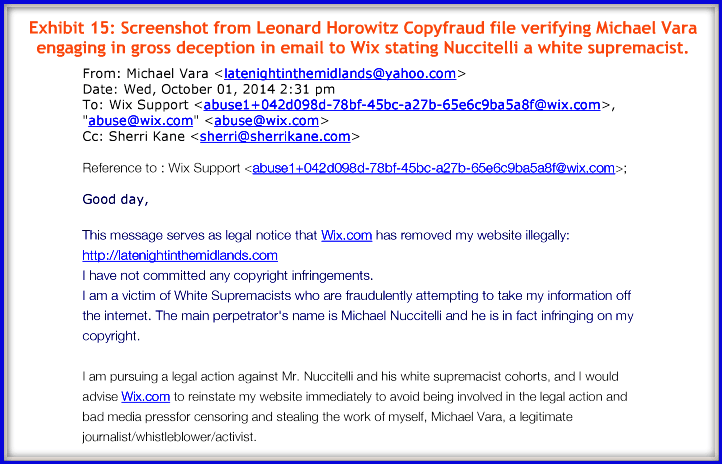
EXHIBIT-15: E-15 is a screenshot image, collected from Dr. Leonard Horowitz and Sherri Kane’s copyfraud, defamation, & nefarious files of a Michael Vara email to the website development and hosting company, Wix. Dated October 1, 2014, Michael Vara is responding to Wix in an attempt to restore his LNM website after they shut it down for multiple breaches of their community guidelines. In the short email, Michael Vara again engages in disinformation by stating I am a white supremacist attempting to steal his information off the internet.
As you can see, he also adds that I am in league with other cohorts in which he has had to secure legal representation. If you’ve read some of the other exhibits above, I think you’ll agree a pattern has been established proving how often and outlandish Michael Vara uses deception and defamatory information about others to cloak and minimize his nefarious intentions. Posted on this list and throughout this article, please know I’ve only presented a small sample of evidence illustrating Dr. Leonard Horowitz, Sherri Kane and Michael Vara’s nefarious and bizarre behaviors.
Hidden LNM Public Dear Disciplinary Link
http://latenightinthemidlands.com/dear-disciplinary-board/ (successfully deleted)
EXHIBIT-16: E-16 is a screenshot image of Michael Vara’s new web page at his LNM Radio Network website he calls, “Dear Disciplinary Board.” As you can see in my image captured on December 29, 2014, this web page provides a direct link to open, review and download Dr. Leonard Horowitz and Sherri Kane’s delusion themed document targeting me and addressed to the NYS Education Department & Office of Discipline. The other two links above the red arrow are an audio phone conversation with Lee Bracker and myself and his documentary he produced presenting the Troll Triad and their deceptive practices. If you enjoy documentaries, provided here is a link to Lee Bracker’s hour long investigative report about the Troll Triad. It is very well done and Mr. Bracker is quite talented at investigative reporting and video production.
Link: Mark of the Frequency Beasts

EXHIBIT-17: E-17 is a screenshot image thanking YouTube for deleting Michael Vara’s August 28 & August 29, 2014 LNM Radio Shows. These two shows were the flashpoints that triggered my adversarial relationship with Michael Vara, his listeners, and associates. It was during these two shows where Michael Vara read my private emails, disclosed private information about myself and habitually spewed lies live on air. If interested in learning more about how the Troll Triad came to target iPredator Inc. and myself, provided here are links to sequential web pages and blog posts I authored presenting their preposterous accusations and disinformation tactics.
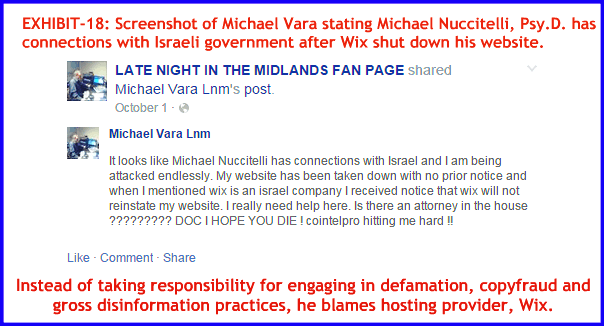
EXHIBIT-18: E-18 is a screenshot image from a Facebook comment on October 1, 2014 made by Michael Vara. As you can see, he writes I have connections with the Israeli government. Knowing Wix is an Israel-based company, Michael Vara somehow holds me responsible for having his website shut down. I have no way of knowing why Wix shut down his site. I can only assume that he refused to remove hate speech themed content and copy written materials authored by me and Wix had enough of his habitual breaches of their terms of service and guidelines.
Michael Vara moved his website to the same internet domain company, Internet.bs Corp., as Dr. Leonard Horowitz and Sherri Kane did with their websites. What is typical bloviating by Michael Vara; he disparaged Wix on numerous occasions both on air and throughout his social networking sites. From scanning through my database, I stopped counting at seventeen where he either wrote or verbalized on air how he longs to sever all ties with Wix. As we now settle into 2015, Michael Vara has not only not kept his word again, but he actually changed his crippled site Wix gave back to him and now uses it for what he calls his Wall of Shame and Troll Man site. Provided here are the links if interested in viewing the nonsense he’s created.
LNM Hidden Wall of Shame Link http://latenightinthemidlan.wix.com/lnm-radio#!wall-of-shame-/cao2
LNM Wix Redacted Troll Man Page http://latenightinthemidlan.wix.com/lnm-radio#!troll-man-lnm/c1zkm
LNM Wix Website Homepage Link http://latenightinthemidlan.wix.com/lnm-radio
(all successfully deleted)
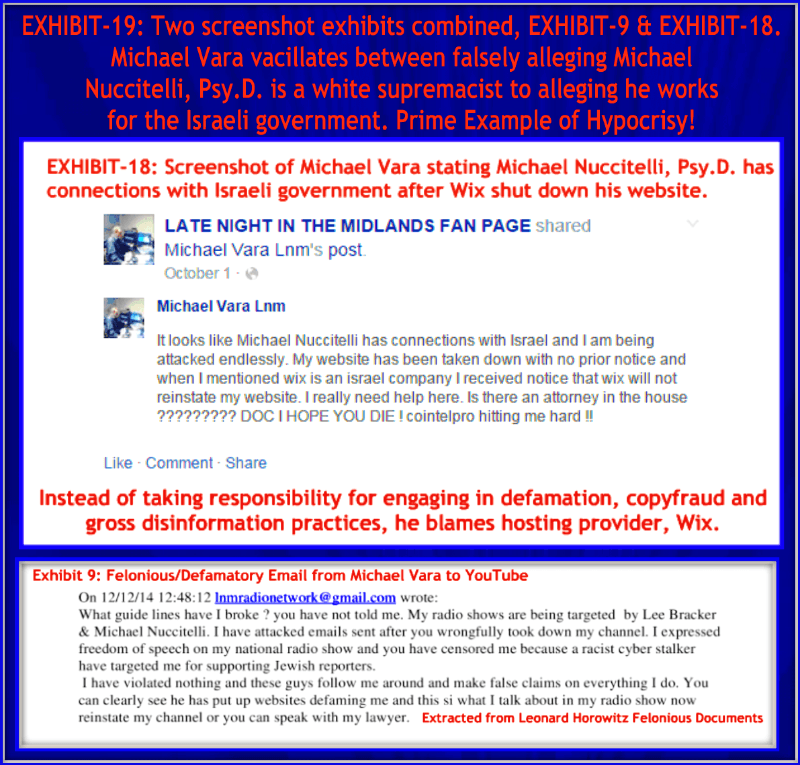
EXHIBIT-19: E-19 is a screenshot image of two screenshot exhibits combined, EXHIBIT-9 & EXHIBIT-18, posted and disseminated by Michael Vara within an eight-week period from October-December 2014. The hypocrisy illustrated in these two images is amazing. Michael Vara vacillates between falsely alleging I’m a white supremacist to saying I work for the Israeli government. This image alone illustrates how he changes his patterns of deception and disinformation frequently. What’s most intriguing is that none of his listeners, associates or loved ones ever confront him about his habitual patterns of lies and derogatory statements. One does not have to be a forensic psychologist, investigative journalist or private detective to piece together quickly his pathological patterns of lying.
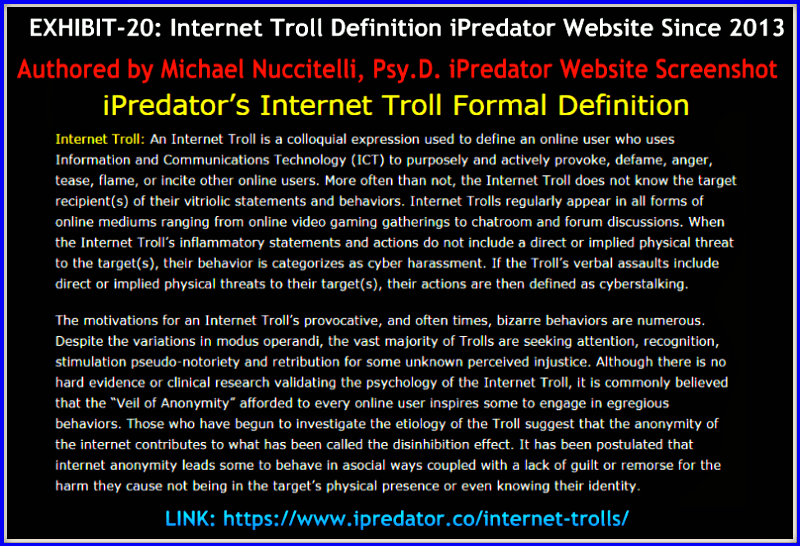
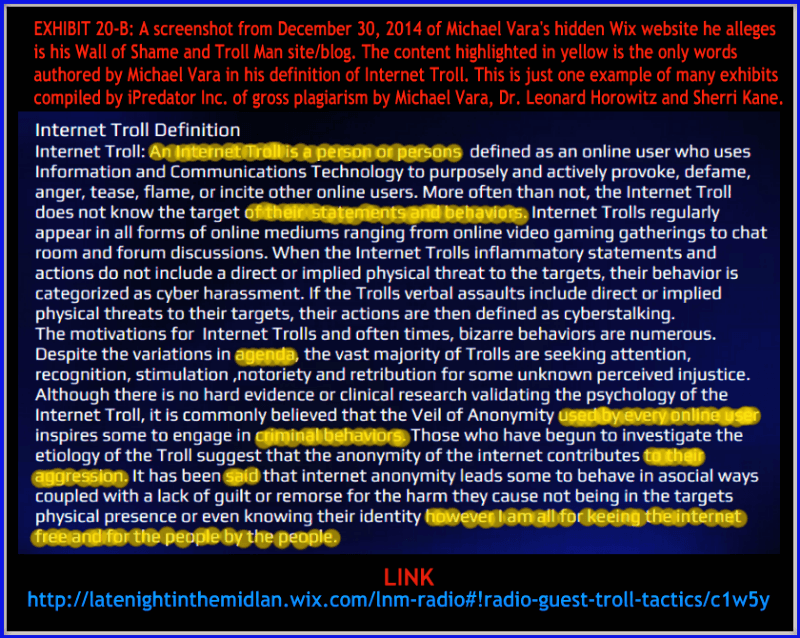
EXHIBIT-20: E-20 is a screenshot image of my formal Internet Troll definition from the iPredator website I authored back in 2013. This same definition I’ve used in multiple posts, pages, social networking site posts and emails to online users and students seeking information on Internet Trolls. The second image, EXHIBIT 20-B, is a screenshot captured from December 30, 2014 of Michael Vara’s hidden Wix website he alleges his Wall of Shame and Troll Man blog. The content highlighted in yellow are the only words authored by Michael Vara. This is just one example of many exhibits compiled illustrating Michael Vara, Dr. Leonard Horowitz and Sherri Kane engages in gross copyfraud and plagiarism. As of January 5, 2015, it is live and available for review by visiting his hidden page.
Link: LNM Radio Guest Troll Tactics (successfully deleted)
EXHIBIT-21: E-21 is a simple image I created to verify that Cyber Tyger and Troll Man are owned by iPredator Inc. and I. Both of my pediatric internet safety characters are formally copy written with the United States Copyright Office in Washington D.C. The term is called Copyfraud and Michael Vara, along with help from Dr. Leonard Horowitz and Sherri Kane, have launched a campaign stating Michael Vara is the owner of Troll Man. The amount of time, effort and frustration the Troll Triad created for me was extensive, to say the least.
However, their deceptive tactics only fooled their minions and blind faith followers. If you plan on creating a product, service or concept new to humanity, I strongly recommend you first read the Digital Millennium Copyright Act of 1998 and the DMCA US Copyright Office Summary before announcing it online. I’ve pasted below both documents to read and download. Lastly, for my gratification, I’ve also once again pasted the copyright ID’s for my pediatric internet safety characters, Cyber Tyger, and Troll Man. When they are ready to be released, they will be public domain and free to use by anyone seeking to introduce young children to internet safety. I created these two characters to be free educational tools, and they will remain that way.
- Link: Digital Millennium Copyright Act-1998
- Link: DMCA-U.S. Copyright Office Summary
- Troll Man: U.S. Copyright #1-1796196711
- Cyber Tyger: U.S. Copyright #1-1825203061
“Society has now become ripe for the birth and growth of a new human predator advanced in all things Internet. This assailant’s name is iPredator.” Michael Nuccitelli, Psy.D. (2011)
Troll Triad is an online assailant and group dynamic concept that introduces a three-pronged archetypal model defining groups of online users who engage in defamation of character, slander & character assassination. Troll Triad is also a conceptual framework and template describing how future groups of successful iPredators will be partitioned into three archetypal segments. This troika includes the Cerebral, Provocateur and the Crier. When these three elements mix correctly, the Troll Triad becomes a masterpiece of human predation alchemy.
Michael Nuccitelli, Psy.D.
Michael Nuccitelli, Psy.D. is a NYS licensed psychologist, cyberpsychology researcher and online safety educator. In 2009, Dr. Nuccitelli finalized his dark side of cyberspace concept called iPredator. Since 2010, he has advised those seeking information about cyberbullying, cyberstalking, cybercriminal minds, internet addiction and his Dark Psychology concept. By day Dr. Nuccitelli is a practicing psychologist, clinical supervisor and owner of MN Psychological Services, PLLC. After work and on the weekends, he volunteers helping online users who have been cyber-attacked. Dr. Nuccitelli’s is always available to interested parties and the media at no cost. This website and everything created by Dr. Nuccitelli is educational, free and public domain.
iPredator Inc., https://ipredator.co, does not represent or endorse the accuracy or reliability of any information, content or advertisements contained on, distributed through, or linked, downloaded or accessed from any of the services contained on this web page or website, nor the quality of any products, information’s or any other material displayed, purchased, or obtained by you as a result of an advertisement or any other information’s or offer in or in connection with the services herein. You hereby acknowledge that any reliance upon any materials shall be at your sole risk. iPredator Inc., https://ipredator.co, reserves the right, in its sole discretion and without any obligation, to make improvements to, or correct any error or omissions in any portion of the service or the materials.